North Carolina schools, local governments try to stave off wave of ransomware attacks

PITTSBORO, N.C. (WTVD) -- The crimes may be sophisticated but what the cyber crooks are after is rather simple: money.
"These are global threat actors," Dan LaMontagne, Chatham County Manager, told ABC11. "This is not some local teenager in his basement. This was a large organized crime organization."
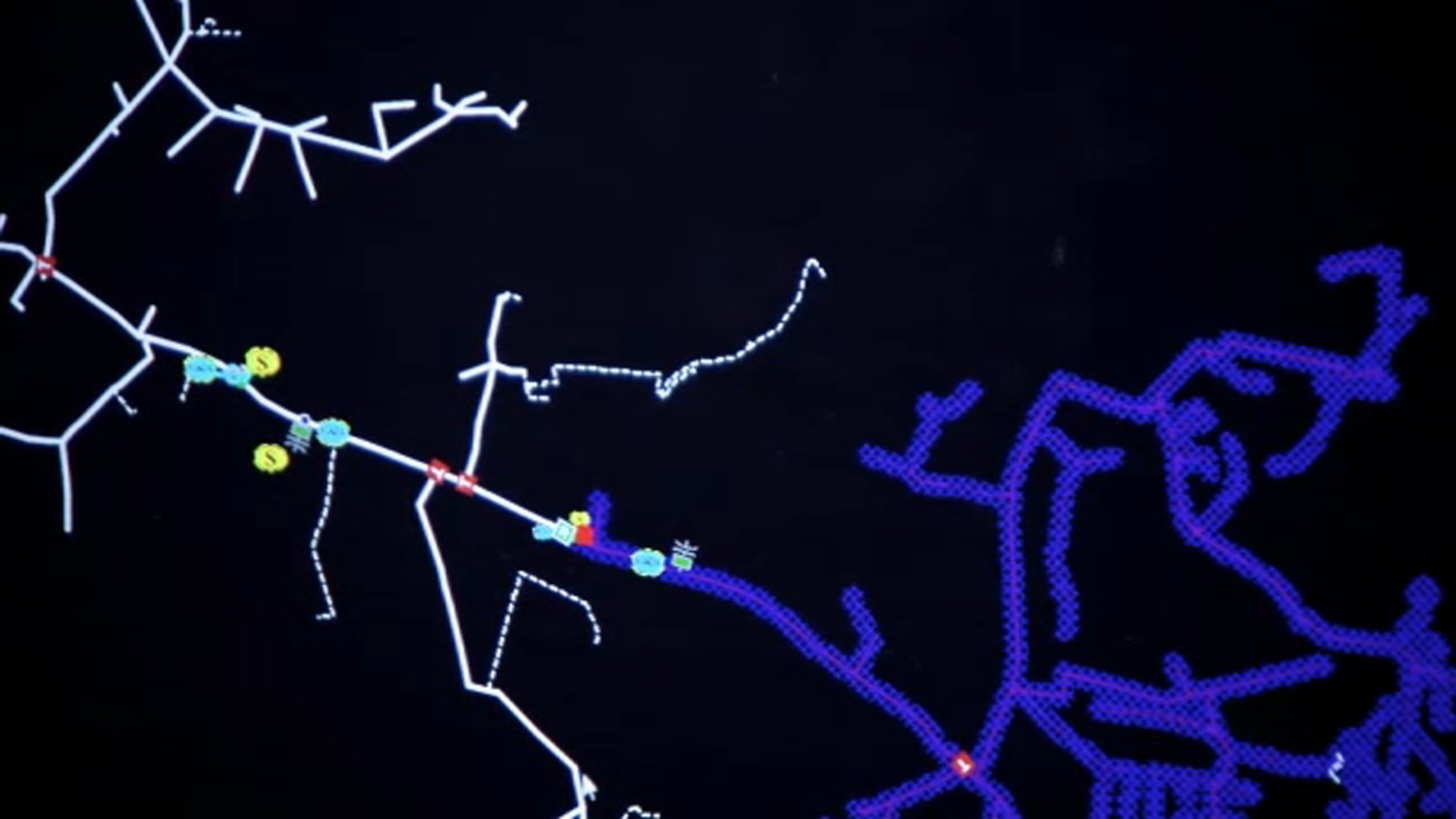
LaMontagne and the entire Chatham County staff know firsthand the stressful experience of being under attack; on Oct. 28 2020, hackers swarmed the county network and held it hostage for 50 Bitcoin, which today is worth up to $2 million. The "ransomware" attack took away the county's use of its computers, internet access, phones and voicemail.
"It's really difficult to be dealing with these two extreme situations at the same time," LaMontagne said, referring also to the COVID-19 pandemic. "Just think of social services and all the activities with foster care, with food stamps. With our council on aging that helps with our aging population, with our development services we still have development throughout the pandemic. Our 911 center was also affected by this, our sheriff's department. So we were able to adapt fortunately but it certainly caused stress for myself and all of our staff."
Subsequent FBI investigations would tie the attack to cyber gang called DoppelPaymer.
"Since late August 2019, unidentified actors have used DoppelPaymer ransomware to encrypt data from victims within critical industries worldwide such as healthcare, emergency services, and education, interrupting citizens' access to services," the FBI says in a bulletin published in December 2020. "Since its emergence in June 2019, DoppelPaymer ransomware has infected a variety of industries and targets, with actors routinely demanding six- and seven-figure ransoms in Bitcoin. Prior to infecting systems with ransomware, the actors' exfiltrate data to use in extortion schemes and have made follow-on telephone calls to victims to further pressure them to make ransom payments."
Nearly five months after the attack, LaMontagne continues to manage a complete overhaul of Chatham County's digital infrastructure, including new domains for email and a website.
"The think I've learned from this really is that it's not a matter of if you will be under attack from something like this it's when."
Ransomware attacks hit across North Carolina
Maria S. Thompson, North Carolina's State Chief Risk Officer, refers to the data contained in government networks that criminals are accessing as "low hanging fruit," and is a key leader of a joint cyber task force of state and federal partners that's on both offense and defense against ransomware attacks.
"Sometimes it's easy to blame that a user clicked on a link in an email, but in some cases it was a misconfigured device that they were able to compromise," Thompson told ABC11.
In a NCDIT report obtained by the I-Team, officials confirmed at least 17 ransomware attacks throughout North Carolina in 2020, including Orange County. The other targets included four more counties, three cities, one town, five public school districts and three colleges and universities.
"We don't pay," Thompson said. "We hold strong that the thought that if you pay you continue the cycle and your data is already severely compromised."
The DIT offers several suggestions for protecting networks at home, at work and at school:
- Defense in Depth: Firewalls, antivirus, and endpoint detection/response solutions
- Network penetration testing
- Cybersecurity audits
- Computer use, device, and password policies
- Access management and control policies and procedures
- Email security solutions (such as anti-phishing solutions, spam filters, email
- Signing certificates (S/MIME certificates)
- Employee cybersecurity awareness training and phishing simulations
- Incident response and disaster recovery plans
- Use of .gov domain for public facing web servers
- Current data OFFLINE backups